On Thursday, December 9th, the internet was turned upside down by news of a Remote Code Execution (RCE) vulnerability in a package named Log4j. Log4j is a logging framework commonly used by programs written in the programming language Java. An RCE is the highest level of security flaw — it means that an arbitrary hacker on the internet can run their code on your computer.
Understandably, there was a lot of alarm about this security threat, and we received questions regarding whether or not OneSignal was exposed. We're glad to report that OneSignal was almost completely unaffected by this issue.
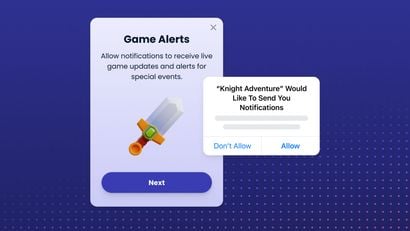
To evaluate our risk, we looked into two main areas that could potentially be of concern based on the nature of the threat. First, we reviewed the SDKs that our customers use to easily integrate our product with theirs. Only one of our many SDKs (the Android mobile SDK) is written in Java . However, this SDK does not use Log4j and was never vulnerable to a security breach.
Secondly, we looked into the extensive back-end infrastructure that runs our website, APIs, and all our custom services. If we had any internet-connected programs that used Log4j, this infrastructure could be at risk. Thankfully, we do not have any programs that are impacted. We have never written our server-side code in Java, so none of our code was directly vulnerable.
As an additional security measure, we scanned all of our production servers for Java programs that contained Log4j. In our Business Intelligence infrastructure, we discovered that we were using three third-party Java programs that contained vulnerable versions of Log4j. We immediately patched these programs and are confident that we do not have any further exposure to these issues.
If you still have questions about Log4j or want to better understand how we protect your data, we're here to help. Get in touch with our team at support@onesignal.com.